Services & Solutions
IT Governance
Since its initial stages, Information Technology (IT) has played the role of technology provider by supporting companies to perform their services more efficiently and effectively. Over the years, IT has become the backbone of companies, without it today it would be impossible for most companies to move forward (less than ever to be successful). As a result of its growing weight in the company, the IT function is transforming itself from a simple technology supplier to becoming a strategic partner.
In this evolutionary process, IT organizations generally follow a three-step approach in which each stage builds on the previous one, as illustrated in Figure 1.
 Figure 1: Evolution of the IT Function within organizations
Figure 1: Evolution of the IT Function within organizations
IT Infrastructure Management (ITIM)
During this phase, IT organizations focus on improving the management of corporate infrastructure. Effective infrastructure management means maximizing the performance of IT resources and taking control of the infrastructure, the devices it contains and the data it generates.
IT service management (ITSM)
The next stage sees IT organizations actively identify the services that customers need and focus on planning, provisioning and service levels to meet availability, performance and security requirements and achieve quality goals at agreed costs.
IT Governance (ITGOV)
In the more mature phase, IT organizations evolve into IT value management, transforming themselves into real business partners who support the company in the development of new business opportunities. In this phase, IT processes are fully integrated into the business processes life cycle, improving service quality and business agility.
Through these changes, IT as a component necessary for survival becomes a success factor, an opportunity to differentiate and obtain a competitive advantage.
Table 1 illustrates the different perception that the Business Divisions have of the IT contribution, in the process of transformation from Service Provider to Strategic Partner:
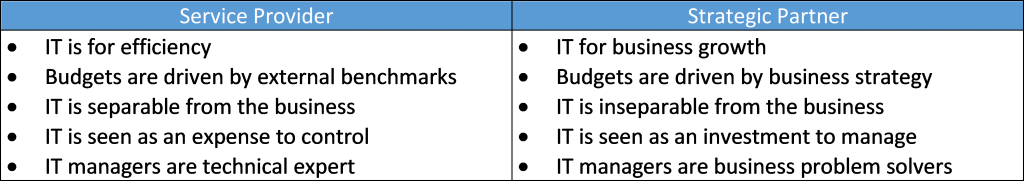
Table 1: (N. Venkatraman – CSC) IT as Service Provider or as Strategic Partner
Application Delivery Management
A project can be considered as a set of activities and tasks characterized by the following properties:
- a well-defined goal to be achieved by respecting certain specifications
- a predetermined start and end date
- a pre-established budget
- a number of resources identified a priori
The SW industry is full of projects’ examples that do not meet the expectations defined in the initial phase:
- projects which cost much more than estimated and which are completed later than expected
- projects that do not end because the complexity has not been managed
- projects that, although formally concluded, in the field test prove inadequate to meet customer expectations
The causes can be innumerable, but they have a common root: a management not supported by effective methods.
A project initiative usually starts from an internal requirement in the customer’s business process, and must be tackled by distinguishing two aspects:
- Management process (Project Management)
- Technical process (SW engineering)
The management process is well defined and declined in its various aspects by the Project Management Institute in the PMBOK, while the technical process has been addressed by the regulations defined by the IEEE Computer Society and over the years has led to the definition of multiple approaches, each of which certainly has many strengths but also some flaws; the choice of the most suitable approach should always be based on the specific characteristics of the project initiative, as recalled by the UNI EN ISO 9000: 2015 standard, and as the market imposes when it asks for a predefined ability to respond to ever new problems and always more uncertain.
An operational hypothesis to reach the definition of SW processes in an Organization can be summarized with:
- Strategic business management
- Governance of the organizational structure
- Acquisition of the SW methodology
In an organization attentive to the innovation of its technology, the company methodology (business strategy) necessarily precedes and hosts the SW methodology (product realization strategy): you therefore enter the Top Management ‘s sphere of responsibility.
The definition of the sw processes must therefore be seen as a flexible production system, developed in accordance with the business strategy.
Our professionals, in addition to the many years of experience acquired in the management of highly complex projects and programs, also have a deep knowledge of Project Management best practices, certifications on the main methodologies (PMP, Agile Scrum Master), and excellent knowledge of the Microfocus portfolio’s solutions for Application Delivery Management (ADM), which are market leaders in the primary and support processes described below.
Security Governance
We think of a modern programming and management of security that takes into account how the risk is originated, what actions generate reactions, and who for the benefits obtained and skills must be responsible for management. In order to follow this line, a widespread political and corporate culture of risk management is needed, recognition of the complexity of the various activities or initiatives put in place, training and updating of professionals who are able to manage complexity, a shared approach by of all interested professionals. Taken from: “Complexity of security and risk management”
By now, information and communication technologies have taken on a fundamental role in the definition and management of processes and activities within an organization. Thanks to technologies, data and information can be transmitted, archived, processed, recovered and shared between different systems, quickly and automatically.
To use these functions safely, it is necessary to ensure that during its management the data maintains a set of characteristics, such as confidentiality, integrity and availability. By respecting this combination of parameters, it is possible to contrast the exposure of the data to risks, threats and vulnerabilities, which can cause a loss of information and thus cause reputational damage at company level.
“Security Governance” provides a set of tools, processes and technologies with which the company is able to perform prevention, detection and response activities to cyber attacks. The “Security Governance” must not be addressed only from a technological point of view, the involvement of people and the definition of appropriate processes in order to:
- have a widespread corporate culture of politics and risk management;
- recognize the various security complexities inherent in the activities or initiatives implemented;
- train and update professionals for the management of this complexity;
- have a methodology shared by all interested professionals.
Our company, ISO 27001 certified, is able to support you in all phases of the safety management process, in compliance with industry standards / regulations and in parallel with your company business strategies.
Our professionals, in addition to the many years of experience gained in the management of highly complex corporate security, also have a profound knowledge of the sector regulations and standards (GDPR, PCI DSS, NIST) and certifications of specific methodologies (COBIT®, TOGAF® , ISO / IEC 20000, ISO / IEC 27001, CISSP), and an excellent knowledge of the solutions of the Microfocus portfolio, market leader in the field of Security Governance processes.
Digital Transformation
In the transformation process from a simple technology supplier to a strategic partner, the contribution of the IT function to defining the transformation strategies of the corporate business will become increasingly significant; the focus of the CIO will shift from the management of systems that support business operations to the creation of systems that define the organization. The CIO will therefore have to expand its mental models to be successful in this planning and transformation. For decades, systemic thinking has been the decisive paradigm that has driven IT departments focused on engineering in designing solutions. Moving forward, new paradigms such as Theory of Constraints will need to be understood and woven into IT operations in order to provide a successful solution for a hyper-complex digital economy.
Translated from Digital Business Transformation Strategy Needs a Change of Perspective – Gartner
Digital transformation is perhaps the most important trend of our time, almost a digital revolution.
And like all (r)evolutions, even the digital one can bring enormous advantages: redesign and simplify processes, reduce redundancies and errors related to non-strategic manual activities, improve integration between all company stakeholders, generate greater efficiency, better operation, reduction of time and costs, using a combination of different technological solutions.
The list of technological solutions grows and updates daily with increasingly advanced and integrated systems, according to an approach aimed at reasoning for maximum convergence between systems and information flows, which run through networks, passing from the Web: automation, computerization, virtualization , cloud, mobile, Unified Communication and Collaboration, Internet of Things…. All this, with the possibility of combining the offline world with the online world, managing infrastructures, systems, applications and services in an extremely more flexible and dynamic way, thanks to the new logic of As a Service and Pay per Use inaugurated by the increasingly driven evolution of virtualization and the cloud
But digital (r)evolution can also generate resistance, opposition, rejection, as happens for all important changes, because they produce insecurity, instability, fears.
Engage innovation paths, both for large companies and SMEs, means reviewing internal operational processes and procedures for interacting with customers and suppliers, designing new digital products and services, broadcast on new online and offline channels, gain analytical skills of digital data.
Our company is able to support you in all phases of the digital transformation and innovation process, in parallel with your business strategies.
Our professionals, in addition to years of experience in highly complex digital transformation paths of business realities, they also have a deep understanding of the key technologies, as well as an excellent knowledge of the Microfocus solutions portfolio, the market leader in the field.
AI Solutions
The current PJC portfolio includes the following solutions:
AIVA (Artificial Intelligence for Video Analysis) includes the best basic features of the Artificial Intelligence algorithms for video analysis. The composite management of these skills, driven by a great mastery of Data Science techniques, allows us to build ability to recognize complex situations, actions, mutual correlation between objects and people, flows.
SPHERA (Systems Prediction and Health Rate Analyzes) is the Artificial Intelligence solution proposed by Project Consulting for predictive maintenance and optimization of hardware resources in data centers. SPHERA uses current monitoring systems to collect data from agents and sensors located in the data center.

AIDA-SHM (Arificial Intelligence Data Analyzer – Structural Health Monitoring) – The data science approach is the basis of the AIDA-SHM IoT solution. Multimodal and multimedia data from a region of interest are collected, integrated, analyzed with Artificial Intelligence techniques for the monitoring, interpretation and continuous prediction of bridge and viaduct parameters.

PAMINA (Platform for Integrated Multimedia Analysis in Applied Neurosciences) is the solution to collect, integrate, process, manage and present data and metadata generated in a modern neuroimaging laboratory according to an innovative interaction model, which guarantees organizational flexibility, offering in a the only solution is the use of technology in the most productive way.




